This article is based on the study written by Alexandre Pujol (Linux Systems and Security Engineer) within the OSSA team led by Gaël Lago.
Within LINAGORA there is what some call our last bulwark against chaos: the OSSA department for Open Source Software Assurance. Behind this name lies a very real mission: to provide support and maintenance for all open‑source software.
A core part of their work is helping organisations make the right choices. This involves continuous monitoring, analysis, and recommendation. It is in this context that we conducted a study dedicated to security bastions. Why this topic? Because in information systems where accesses multiply and identity becomes the new security perimeter, the bastion is, and will remain, a central piece.
1. The bastion remains a pillar of access control, and we recommend treating it as such
In modern infrastructures, the bastion acts as a controlled entry point between administrators and critical systems. All sensitive connections pass through it: access to servers, databases, or production environments.
This role allows the control and traceability of accesses to be concentrated in a single place. Every session can be supervised, recorded, and analysed. Such visibility is essential, whether to understand an incident, satisfy an audit requirement, or detect abnormal behaviour.
But the bastion is not sufficient protection on its own. It adds an extra layer to the architecture and must be correctly integrated and maintained. Mis‑configured, it can become a weakness itself. Therefore it should be regarded as one component among many, within a broader security strategy.
2. What we advise you to require from a modern bastion
OSSA’s monitoring work shows that a bastion is never isolated. Its effectiveness depends directly on its ability to integrate with the existing ecosystem.
Identity‑system integration is the first point. Compatibility with LDAP directories and multi‑factor authentication mechanisms centralises access management and avoids the proliferation of local accounts that are hard to maintain and audit. The bastion then becomes a natural extension of the identity system, not an extra silo.
Supervision is the other essential function. A bastion must allow real‑time visualisation of sessions, record connections, and export this information to monitoring tools or a SIEM. This logging capability is indispensable for incident investigation, compliance reporting, or simply understanding what happened on a system.
Interoperability with modern infrastructure tools is also a decisive factor. Integration with secret managers or DevOps tools embeds the bastion into existing operational practices without breaking workflows.
Finally, the study highlights a more counter‑intuitive point: command restriction directly on the bastion. This feature is often seen as an important security element, theoretically preventing administrator errors, data exfiltration, or the execution of malicious commands.
In practice, its effectiveness is very limited. As Alexandre Pujol notes in his analysis, such mechanisms usually rely on command filtering, often based on regular expressions, that can be easily bypassed. For example, a forbidden command like rm -rf data/ can be encoded and executed in another form:
echo cm0gLXJmIGRhdGEvCg== | base64 --decode | sh
The original command is no longer visible to the bastion, and the action is not blocked.
These considerations should guide the choice of a solution that fits your context and priorities.
3. Existing solutions: what we recommend and the vigilance points
OSSA’s watchfulness reveals a clear reality: to date, no open‑source solution fully meets all identified requirements. This does not mean that there are no good options; rather, every choice involves trade‑offs that must be understood.
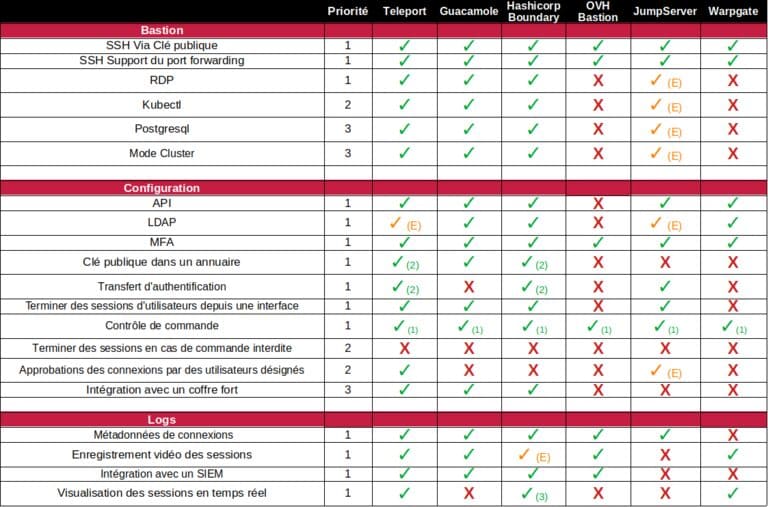
Among the tools analysed (Teleport, HashiCorp Boundary, Apache Guacamole, OVH The Bastion, JumpServer, and Warpgate), Teleport currently appears the most mature functionally. Its modern architecture, use of certificates for access management, and deep integration with existing infrastructures make it a reference. It satisfies most of the operational needs organisations face.
However, this maturity comes with a significant limitation: key features, especially LDAP integration, require an enterprise licence. This raises a question beyond pure technical aspects: governance and control of the tool. Can we still speak of a fully open‑source alternative when essential building blocks depend on a commercial offering?
Given this, Apache Guacamole stands out as the most obvious open‑source alternative. Completely free, it enables the construction of a bastion without reliance on proprietary features. This choice gives total mastery over the solution and its behaviour. Nevertheless, this freedom carries an operational cost: Guacamole provides the necessary bricks, but you must design and maintain a broader architecture around it to meet the full set of requirements.
Between these two approaches, the study also points to emerging projects that look particularly promising, Warpgate among them. The software already satisfies several of the functional requirements identified, with a modern approach aligned with current practices. It is still immature, but its positioning and technical choices make it a solution to watch closely. At this stage, our recommendation is less to deploy it immediately than to monitor its evolution actively.
This observation illustrates a broader truth about open source: solutions exist, they evolve, and they improve thanks to usage and contributions.

Conclusion : Sometimes the best recommendation is to contribute
OSSA’s role at LINAGORA is to help organisations understand the open‑source ecosystem and make informed choices, based on concrete analyses such as this bastion watch.
These works show that good solutions are available today, but they also reveal limits, trade‑offs, and projects still in development. In this context, monitoring is only the first step. Open source thrives on contributions—from those who improve existing tools or propose new approaches.
In that spirit, our security and identity expert Xavier Guimard launched Open Bastion. This open‑source project aims to address current access‑control challenges, with direct integration into identity systems, notably LemonLDAP::NG.
The project is available here
If you wish to discuss these topics with our teams, benefit from our experience, or receive guidance on your choices, the OSSA team is at your disposal.
The complete study by Alexandre Pujol on bastions can be found here


